
Post-Quantum Cryptography: Quantum Computers Will Break Today’s Encryption – Are You Ready?
Today’s encryption will not survive quantum computing. It was never designed to.
When large-scale quantum systems become viable, widely used algorithms like RSA and elliptic-curve cryptography will fail—not gradually, but all at once.
The risk is already in motion. Attackers can capture encrypted data today and decrypt it later when quantum capabilities catch up. It has a name: harvest now, decrypt later. Encryption that cannot be broken today is increasingly likely to be broken within the next decade, and much of the encrypted data being collected now will still be sensitive when that happens.
Why post-quantum cryptography matters now
Post-Quantum Cryptography (PQC) requires organizations to move to new, quantum-resistant algorithms. These are not simple or quick changes for most businesses. Cryptography is embedded into every layer of the software stack—from applications to infrastructure to core dependencies—and is often hard-coded into legacy systems that are difficult and costly to change. Updates can also have downstream impacts on performance and load calculations.
To prepare, organizations need to build a clear picture of where cryptography exists across their environments. That means creating a new kind of bill of materials to inventory and track cryptographic implementations, and becoming more crypto-agile so updates can happen more routinely as standards evolve.
Auditing where cryptography exists—and understanding the shelf lives of sensitive data—helps organizations prioritize their early efforts. Data that needs to remain secure for years is already exposed to harvest now, decrypt later attacks. In many cases, the algorithms protecting that data today will take time to replace, especially as changes need to propagate through complex systems and supply chains.
Regulatory pressure is accelerating the timeline
Regulators are setting concrete timelines that make post-quantum cryptography a near-term engineering concern—not a theoretical one.
In the U.S., the CNSA 2.0 program from the National Security Agency (NSA) mandates a phased transition to post-quantum cryptography, with key deadlines beginning in 2027 and major migration milestones by 2030.
In Europe, frameworks such as the NIS2 Directive and the Digital Operational Resilience Act (DORA) require organizations to assess cryptographic risk, enforce stronger cryptographic controls, and demonstrate readiness to evolve toward quantum-resistant approaches.
PQC is no longer a distant concern. It is already on compliance roadmaps.
Securing the transition to post-quantum cryptography
The shift to post-quantum cryptography goes beyond a technology upgrade, and introduces a fundamental change in how software is built, validated, and governed.
As AI-assisted development accelerates, development teams need confidence that cryptographic patterns are applied correctly and consistently. This depends on visibility into how code is created and clear validation that secure practices are followed across workflows.
AI can assist in generating and reviewing code, but it does not guarantee secure outcomes. Validating implementations and reinforcing secure patterns still needs to be part of everyday development.
AI Software Governance connects visibility, risk correlation, and developer capability. Secure Code Warrior provides visibility into AI-generated code, correlates risk at commit, and strengthens developer capability through hands-on secure coding learning. Together, this enables organizations to adopt post-quantum cryptography while maintaining control as development becomes increasingly AI-assisted.
New post-quantum cryptography learning in Secure Code Warrior
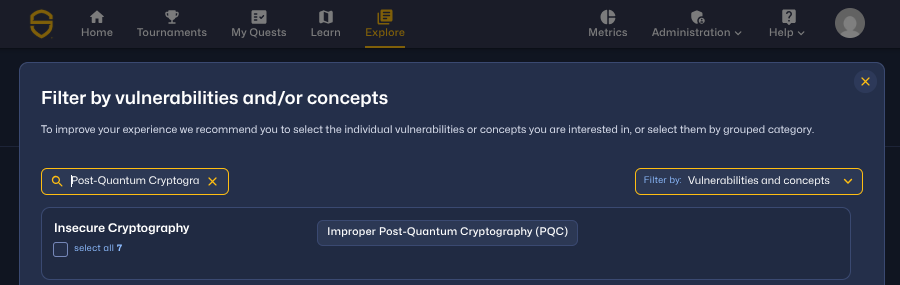
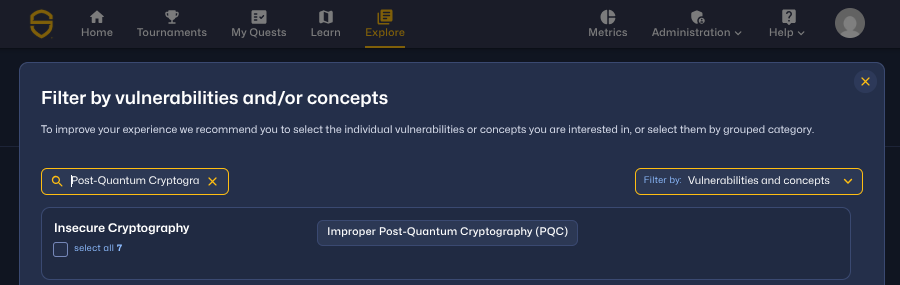
To support this transition, Secure Code Warrior has introduced a new vulnerability category: Improper Post-Quantum Cryptography (PQC).
New learning topics are available across ten languages and frameworks, including Terraform (AWS and GCP), Python, Java, Java Spring, C# (.NET Core and Basic), JavaScript and TypeScript (Node.js Express), and Go. Cloud and backend infrastructure are where early PQC efforts are most urgent, and where most organizations will find their most critical cryptography components.
Each topic includes language-specific guidance, hands-on AI Challenges, and real-world scenarios that simulate PQC implementation risks. This gives developers practical experience with how quantum-safe cryptography is implemented and where it can fail.
Post-quantum readiness requires teams to understand where cryptography exists in their code, how PQC impacts implementation, and how to apply secure patterns consistently across development. As quantum-resistant approaches begin to appear in modern standards, teams must also validate how they are applied in real code. Clear visibility into development workflows, combined with reinforcement of secure practices, helps reduce software risk at the source and maintain control as development becomes increasingly AI-assisted.
You can find the new PQC topics in Secure Code Warrior across Quests, Learn, and Explore. Start building the developer capability required to secure what comes next.

Post-quantum cryptography (PQC) is critical for protecting data from quantum computing threats. Learn how “harvest now, decrypt later” exposes risk and how developers can prepare for quantum-safe security.
Shannon Holt 是一名网络安全产品营销人员,具有应用程序安全、云安全服务以及 PCI-DSS 和 HITRUST 等合规标准方面的背景。

Secure Code Warrior 您的组织在软件开发全生命周期中保护代码安全,并营造将网络安全置于首位的企业文化。无论您是应用安全管理员、开发人员、首席信息安全官,还是任何与安全相关的工作人员,我们都能助力您的组织降低不安全代码带来的风险。
预约演示Shannon Holt 是一名网络安全产品营销人员,具有应用程序安全、云安全服务以及 PCI-DSS 和 HITRUST 等合规标准方面的背景。
Shannon Holt 是一位网络安全产品营销人员,拥有应用安全、云安全服务以及 PCI-DSS 和 HITRUST 等合规性标准方面的背景。她致力于让安全开发和合规性对技术团队来说更加实用易行,从而弥合安全期望与现代软件开发现实之间的差距。

Today’s encryption will not survive quantum computing. It was never designed to.
When large-scale quantum systems become viable, widely used algorithms like RSA and elliptic-curve cryptography will fail—not gradually, but all at once.
The risk is already in motion. Attackers can capture encrypted data today and decrypt it later when quantum capabilities catch up. It has a name: harvest now, decrypt later. Encryption that cannot be broken today is increasingly likely to be broken within the next decade, and much of the encrypted data being collected now will still be sensitive when that happens.
Why post-quantum cryptography matters now
Post-Quantum Cryptography (PQC) requires organizations to move to new, quantum-resistant algorithms. These are not simple or quick changes for most businesses. Cryptography is embedded into every layer of the software stack—from applications to infrastructure to core dependencies—and is often hard-coded into legacy systems that are difficult and costly to change. Updates can also have downstream impacts on performance and load calculations.
To prepare, organizations need to build a clear picture of where cryptography exists across their environments. That means creating a new kind of bill of materials to inventory and track cryptographic implementations, and becoming more crypto-agile so updates can happen more routinely as standards evolve.
Auditing where cryptography exists—and understanding the shelf lives of sensitive data—helps organizations prioritize their early efforts. Data that needs to remain secure for years is already exposed to harvest now, decrypt later attacks. In many cases, the algorithms protecting that data today will take time to replace, especially as changes need to propagate through complex systems and supply chains.
Regulatory pressure is accelerating the timeline
Regulators are setting concrete timelines that make post-quantum cryptography a near-term engineering concern—not a theoretical one.
In the U.S., the CNSA 2.0 program from the National Security Agency (NSA) mandates a phased transition to post-quantum cryptography, with key deadlines beginning in 2027 and major migration milestones by 2030.
In Europe, frameworks such as the NIS2 Directive and the Digital Operational Resilience Act (DORA) require organizations to assess cryptographic risk, enforce stronger cryptographic controls, and demonstrate readiness to evolve toward quantum-resistant approaches.
PQC is no longer a distant concern. It is already on compliance roadmaps.
Securing the transition to post-quantum cryptography
The shift to post-quantum cryptography goes beyond a technology upgrade, and introduces a fundamental change in how software is built, validated, and governed.
As AI-assisted development accelerates, development teams need confidence that cryptographic patterns are applied correctly and consistently. This depends on visibility into how code is created and clear validation that secure practices are followed across workflows.
AI can assist in generating and reviewing code, but it does not guarantee secure outcomes. Validating implementations and reinforcing secure patterns still needs to be part of everyday development.
AI Software Governance connects visibility, risk correlation, and developer capability. Secure Code Warrior provides visibility into AI-generated code, correlates risk at commit, and strengthens developer capability through hands-on secure coding learning. Together, this enables organizations to adopt post-quantum cryptography while maintaining control as development becomes increasingly AI-assisted.
New post-quantum cryptography learning in Secure Code Warrior
To support this transition, Secure Code Warrior has introduced a new vulnerability category: Improper Post-Quantum Cryptography (PQC).
New learning topics are available across ten languages and frameworks, including Terraform (AWS and GCP), Python, Java, Java Spring, C# (.NET Core and Basic), JavaScript and TypeScript (Node.js Express), and Go. Cloud and backend infrastructure are where early PQC efforts are most urgent, and where most organizations will find their most critical cryptography components.
Each topic includes language-specific guidance, hands-on AI Challenges, and real-world scenarios that simulate PQC implementation risks. This gives developers practical experience with how quantum-safe cryptography is implemented and where it can fail.
Post-quantum readiness requires teams to understand where cryptography exists in their code, how PQC impacts implementation, and how to apply secure patterns consistently across development. As quantum-resistant approaches begin to appear in modern standards, teams must also validate how they are applied in real code. Clear visibility into development workflows, combined with reinforcement of secure practices, helps reduce software risk at the source and maintain control as development becomes increasingly AI-assisted.
You can find the new PQC topics in Secure Code Warrior across Quests, Learn, and Explore. Start building the developer capability required to secure what comes next.
Today’s encryption will not survive quantum computing. It was never designed to.
When large-scale quantum systems become viable, widely used algorithms like RSA and elliptic-curve cryptography will fail—not gradually, but all at once.
The risk is already in motion. Attackers can capture encrypted data today and decrypt it later when quantum capabilities catch up. It has a name: harvest now, decrypt later. Encryption that cannot be broken today is increasingly likely to be broken within the next decade, and much of the encrypted data being collected now will still be sensitive when that happens.
Why post-quantum cryptography matters now
Post-Quantum Cryptography (PQC) requires organizations to move to new, quantum-resistant algorithms. These are not simple or quick changes for most businesses. Cryptography is embedded into every layer of the software stack—from applications to infrastructure to core dependencies—and is often hard-coded into legacy systems that are difficult and costly to change. Updates can also have downstream impacts on performance and load calculations.
To prepare, organizations need to build a clear picture of where cryptography exists across their environments. That means creating a new kind of bill of materials to inventory and track cryptographic implementations, and becoming more crypto-agile so updates can happen more routinely as standards evolve.
Auditing where cryptography exists—and understanding the shelf lives of sensitive data—helps organizations prioritize their early efforts. Data that needs to remain secure for years is already exposed to harvest now, decrypt later attacks. In many cases, the algorithms protecting that data today will take time to replace, especially as changes need to propagate through complex systems and supply chains.
Regulatory pressure is accelerating the timeline
Regulators are setting concrete timelines that make post-quantum cryptography a near-term engineering concern—not a theoretical one.
In the U.S., the CNSA 2.0 program from the National Security Agency (NSA) mandates a phased transition to post-quantum cryptography, with key deadlines beginning in 2027 and major migration milestones by 2030.
In Europe, frameworks such as the NIS2 Directive and the Digital Operational Resilience Act (DORA) require organizations to assess cryptographic risk, enforce stronger cryptographic controls, and demonstrate readiness to evolve toward quantum-resistant approaches.
PQC is no longer a distant concern. It is already on compliance roadmaps.
Securing the transition to post-quantum cryptography
The shift to post-quantum cryptography goes beyond a technology upgrade, and introduces a fundamental change in how software is built, validated, and governed.
As AI-assisted development accelerates, development teams need confidence that cryptographic patterns are applied correctly and consistently. This depends on visibility into how code is created and clear validation that secure practices are followed across workflows.
AI can assist in generating and reviewing code, but it does not guarantee secure outcomes. Validating implementations and reinforcing secure patterns still needs to be part of everyday development.
AI Software Governance connects visibility, risk correlation, and developer capability. Secure Code Warrior provides visibility into AI-generated code, correlates risk at commit, and strengthens developer capability through hands-on secure coding learning. Together, this enables organizations to adopt post-quantum cryptography while maintaining control as development becomes increasingly AI-assisted.
New post-quantum cryptography learning in Secure Code Warrior
To support this transition, Secure Code Warrior has introduced a new vulnerability category: Improper Post-Quantum Cryptography (PQC).
New learning topics are available across ten languages and frameworks, including Terraform (AWS and GCP), Python, Java, Java Spring, C# (.NET Core and Basic), JavaScript and TypeScript (Node.js Express), and Go. Cloud and backend infrastructure are where early PQC efforts are most urgent, and where most organizations will find their most critical cryptography components.
Each topic includes language-specific guidance, hands-on AI Challenges, and real-world scenarios that simulate PQC implementation risks. This gives developers practical experience with how quantum-safe cryptography is implemented and where it can fail.
Post-quantum readiness requires teams to understand where cryptography exists in their code, how PQC impacts implementation, and how to apply secure patterns consistently across development. As quantum-resistant approaches begin to appear in modern standards, teams must also validate how they are applied in real code. Clear visibility into development workflows, combined with reinforcement of secure practices, helps reduce software risk at the source and maintain control as development becomes increasingly AI-assisted.
You can find the new PQC topics in Secure Code Warrior across Quests, Learn, and Explore. Start building the developer capability required to secure what comes next.

点击下方链接,下载此资源的PDF文件。
Secure Code Warrior 您的组织在软件开发全生命周期中保护代码安全,并营造将网络安全置于首位的企业文化。无论您是应用安全管理员、开发人员、首席信息安全官,还是任何与安全相关的工作人员,我们都能助力您的组织降低不安全代码带来的风险。
查看报告预约演示Shannon Holt 是一名网络安全产品营销人员,具有应用程序安全、云安全服务以及 PCI-DSS 和 HITRUST 等合规标准方面的背景。
Shannon Holt 是一位网络安全产品营销人员,拥有应用安全、云安全服务以及 PCI-DSS 和 HITRUST 等合规性标准方面的背景。她致力于让安全开发和合规性对技术团队来说更加实用易行,从而弥合安全期望与现代软件开发现实之间的差距。
Today’s encryption will not survive quantum computing. It was never designed to.
When large-scale quantum systems become viable, widely used algorithms like RSA and elliptic-curve cryptography will fail—not gradually, but all at once.
The risk is already in motion. Attackers can capture encrypted data today and decrypt it later when quantum capabilities catch up. It has a name: harvest now, decrypt later. Encryption that cannot be broken today is increasingly likely to be broken within the next decade, and much of the encrypted data being collected now will still be sensitive when that happens.
Why post-quantum cryptography matters now
Post-Quantum Cryptography (PQC) requires organizations to move to new, quantum-resistant algorithms. These are not simple or quick changes for most businesses. Cryptography is embedded into every layer of the software stack—from applications to infrastructure to core dependencies—and is often hard-coded into legacy systems that are difficult and costly to change. Updates can also have downstream impacts on performance and load calculations.
To prepare, organizations need to build a clear picture of where cryptography exists across their environments. That means creating a new kind of bill of materials to inventory and track cryptographic implementations, and becoming more crypto-agile so updates can happen more routinely as standards evolve.
Auditing where cryptography exists—and understanding the shelf lives of sensitive data—helps organizations prioritize their early efforts. Data that needs to remain secure for years is already exposed to harvest now, decrypt later attacks. In many cases, the algorithms protecting that data today will take time to replace, especially as changes need to propagate through complex systems and supply chains.
Regulatory pressure is accelerating the timeline
Regulators are setting concrete timelines that make post-quantum cryptography a near-term engineering concern—not a theoretical one.
In the U.S., the CNSA 2.0 program from the National Security Agency (NSA) mandates a phased transition to post-quantum cryptography, with key deadlines beginning in 2027 and major migration milestones by 2030.
In Europe, frameworks such as the NIS2 Directive and the Digital Operational Resilience Act (DORA) require organizations to assess cryptographic risk, enforce stronger cryptographic controls, and demonstrate readiness to evolve toward quantum-resistant approaches.
PQC is no longer a distant concern. It is already on compliance roadmaps.
Securing the transition to post-quantum cryptography
The shift to post-quantum cryptography goes beyond a technology upgrade, and introduces a fundamental change in how software is built, validated, and governed.
As AI-assisted development accelerates, development teams need confidence that cryptographic patterns are applied correctly and consistently. This depends on visibility into how code is created and clear validation that secure practices are followed across workflows.
AI can assist in generating and reviewing code, but it does not guarantee secure outcomes. Validating implementations and reinforcing secure patterns still needs to be part of everyday development.
AI Software Governance connects visibility, risk correlation, and developer capability. Secure Code Warrior provides visibility into AI-generated code, correlates risk at commit, and strengthens developer capability through hands-on secure coding learning. Together, this enables organizations to adopt post-quantum cryptography while maintaining control as development becomes increasingly AI-assisted.
New post-quantum cryptography learning in Secure Code Warrior
To support this transition, Secure Code Warrior has introduced a new vulnerability category: Improper Post-Quantum Cryptography (PQC).
New learning topics are available across ten languages and frameworks, including Terraform (AWS and GCP), Python, Java, Java Spring, C# (.NET Core and Basic), JavaScript and TypeScript (Node.js Express), and Go. Cloud and backend infrastructure are where early PQC efforts are most urgent, and where most organizations will find their most critical cryptography components.
Each topic includes language-specific guidance, hands-on AI Challenges, and real-world scenarios that simulate PQC implementation risks. This gives developers practical experience with how quantum-safe cryptography is implemented and where it can fail.
Post-quantum readiness requires teams to understand where cryptography exists in their code, how PQC impacts implementation, and how to apply secure patterns consistently across development. As quantum-resistant approaches begin to appear in modern standards, teams must also validate how they are applied in real code. Clear visibility into development workflows, combined with reinforcement of secure practices, helps reduce software risk at the source and maintain control as development becomes increasingly AI-assisted.
You can find the new PQC topics in Secure Code Warrior across Quests, Learn, and Explore. Start building the developer capability required to secure what comes next.
入门资源
Trust Agent:AI - Secure and scale AI-Drive development
AI is writing code. Who’s governing it? With up to 50% of AI-generated code containing security weaknesses, managing AI risk is critical. Discover how SCW's Trust Agent: AI provides the real-time visibility, proactive governance, and targeted upskilling needed to scale AI-driven development securely.
OpenText 应用程序安全性的强大功能 + Secure Code Warrior
OpenText Application Security and Secure Code Warrior combine vulnerability detection with AI Software Governance and developer capability. Together, they help organizations reduce risk, strengthen secure coding practices, and confidently adopt AI-driven development.
Secure Code Warrior corporate overview
Secure Code Warrior is an AI Software Governance platform designed to enable organizations to safely adopt AI-driven development by bridging the gap between development velocity and enterprise security. The platform addresses the "Visibility Gap," where security teams often lack insights into shadow AI coding tools and the origins of production code.













.png)

